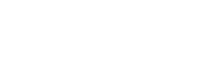
Who doesn't love the promise of shiny new technology?
Better, faster, stronger and smarter than the competition: AI in everything, novel battery chemistries, smart drugs that cure all ills.
Even though we should be immune to the marketing by now, if we’re honest, we all want to believe in magic bullets.
Who doesn’t want quick fixes to make complex problems go away?
With a reassuringly expensive price tag, a sprinkling of the latest magic buzzword, it’s really tempting to believe the hype and imagine that the right product will give us a shortcut to the finish line – whether that’s winning a race or solving a thorny cyber security problem! There's a lot of hype about identity management at the moment, whether that’s identity-related breaches, identity as a foundation for zero-trust, identity as the new perimeter, identity fabrics or other new labels. There is something important behind the hype – the recognition that managing identities is fundamental to a successful cyber security strategy.
There's a lot of hype about identity management at the moment, whether that’s identity-related breaches, identity as a foundation for zero-trust, identity as the new perimeter, identity fabrics or other new labels. There is something important behind the hype – the recognition that managing identities is fundamental to a successful cyber security strategy.
But identity isn’t new! Identity and Access Management (IAM) and Privileged Access Management (PAM) products have been on the market for well over a decade. The principles of Authentication, Authorisation and Accounting (AAA) to enforce who can do what, and keep track of who did what goes back even further.
We’ve been working on these foundational issues for decades, so why do so many organisations still struggle with knowing who has access to what, being able to run governance and compliance processes against that access and what has been done with it?
We commonly see 3 challenges:
1. Your identity problem keeps growing
The expansion and decentralisation of the IT estate from on-prem into multiple public and private clouds mean the scale and complexity of identities, entitlements and activities have exploded. We have to accept that as information systems become more and more embedded in all aspects of human activity there will be ‘more’ of everything.

How do you manage the scaling problem?
Good architecture helps us manage complexity, applying patterns to break systems down into more understandable and manageable units of data and processes. Security has to be built in at this fundamental level, including who (authenticated identities) can do what (authorisation), and who did what (auditing).
The major cloud providers offer a management layer with access models, events and granular APIs so you can define policy and monitor everything. You have all the hooks and data you need, but there's a lot of it and to be manageable you need processes to:
- Group access entitlements into meaningful roles
- Find high-risk log events amongst the noise
- Use all the context cues available to separate trustworthy authentication events from suspicious ones
2. IAM and PAM tools are often under-used and fail to deliver on their promise
Poor quality data makes it difficult to link identities to user accounts; to find owners and approvers for legacy groups and systems with vague names and descriptions, or to understand how (and why) access is granted or being used the way it is.
IAM tools have increasingly added data discovery functionality to help with this issue and clean up your legacy data, but if you have been provisioning cloned access for years, then that same set of cloned access is what the clustering algorithm will find, unhelpfully perpetuating access which is probably far from the least-privilege. The role mining and discovery tools can be useful, but there's still a lot of manual detective work to be done to make a legacy estate presentable to IAM tools in a useful way – just one of the processes needed to get the most out of your investment in IAM/PAM licences.
3. Getting value from your investment in IAM and PAM tools
You have to wrap the technology with the people and processes to provide a service to your organisation. The technology is a tool that has to be tailored and adapted to the needs of each organisation – to the technical landscape, the risk appetite and the regulatory requirements.
All too often we see IAM/PAM implementation projects that have focussed on the technology – buy the tool, install and configure it, and we’re more secure, right? But these tools interact with so much of your infrastructure and have the potential to impact many peoples day-to-day working if implemented poorly. Not to mention that they can give a false sense of security if you have, metaphorically, bolted the front door but left the windows open. Careful thought is needed on how the technology will be used and maintained, and presented to the business in a way it can easily be consumed.
The Target Operating Model (TOM) defines the internal and external elements of the IAM/PAM service.
![]()
Internally, the operational tasks, roles and responsibilities that keep things running day-to-day, but also the strategic tasks that review threats, improve controls, improve efficiency through automation, and review the tooling product lifecycle.
Externally, the IAM/PAM service provides services to the business to help understand and manage identities, access and related risks: to security operations, IT and cloud infrastructure and operations, HR, to GRC, and to the end-users – balancing security and friction to their daily ways of working.
Importantly, the IAM/PAM service has to be consumable, it should be easy for developers and application owners to get their systems and applications on-boarded to identity controls. We want to run a service that makes it easy to ‘do the right thing’ and adopt controls that reduce risk and improve efficiency.
If you're struggling to get value from your IAM or PAM tools, you feel like they've never moved beyond the project stage, or they're stalled because of data quality problems, please get in touch with Savanti at info@savanti.co.uk.
Savanti are identity strategy and implementation experts and help clients at all stages of their security maturity to get better value from the tools they have.
If you want to find out more, visit the chat function on our website: www.savanti.co.uk or fill in the below details: